Tag: Cybersecurity
-
The Complex Debate Over Age Verification on Adult Sites: Solutions, Challenges, and Controversies
In a move that has stirred considerable debate, several prominent adult websites, including Pornhub, have opted to block access in certain states rather than comply with stringent ID verification laws. This development has not only raised questions about the feasibility of such regulations but also ignited discussions around privacy, technology, and the role of government…
-

Navigating the Controversy: The U.S. Ban on Kaspersky Software
The recent decision by the U.S. government to ban Kaspersky software has ignited intense debates around cybersecurity, national security, and even free speech. The heart of the issue lies in whether a software company based in Russia can be trusted on American soil given the current geopolitical tensions. This decision brings to the fore numerous…
-

Cyber Scarecrow: Un’Ombra Leggera nei Confronti del Malware?
Negli ultimi anni, il panorama della sicurezza informatica è stato costellato di innovazioni che promettono di proteggere i nostri dispositivi da minacce sempre più sofisticate. Tra queste innovazioni, Cyber Scarecrow si distingue come un tentativo di creare una soluzione leggera e accesibile per l’utente comune, indirizzato principalmente alla simulazione di strumenti di analisi della sicurezza…
-
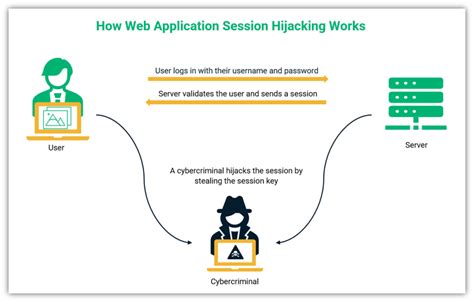
Navigating the Murky Waters of Off-Path TCP Hijacking in NAT-Enabled Wi-Fi Networks: Are We Really Safe?
In the realm of cybersecurity, the phrase ‘off-path TCP hijacking in NAT-enabled Wi-Fi networks’ might sound like a plot straight out of a techno-thriller. However, it is a very real concern, particularly for users who frequent public Wi-Fi hotspots. Despite the advances in security technology, this old yet potent form of attack reminds us that…
-
30 Days Behind Enemy Lines: Running An SSH Honeypot and What I Learned
Operating an SSH honeypot for a month is a revealing yet sobering endeavor. By essentially setting a trap for cyber attackers, you can gain firsthand insight about the myriad of threats your Linux systems could potentially face when ports are exposed to the Internet. This deep dive helps underscore the immense value of cybersecurity protocols…
-
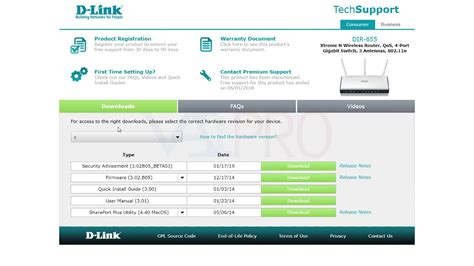
D-Link Routers’ Vulnerability: Malice or Incompetence?
Another major security flaw has been unearthed in D-Link routers, shining a stark light on continued vulnerabilities in consumer networking equipment. An undisclosed factory testing backdoor has been revealed to provide unauthorized telnet access, allowing unauthenticated attackers on the local area network to enable the telnet service by simply accessing a specific URL. This revelation…
-

Why Stronger Information Security Measures Remain a Distant Dream
Despite advancements in technology and the escalating number of data breaches, the prioritization of information security remains a distant dream. While the article provides an accurate depiction of the state of information security, user comments offer a broader landscape of perspectives and challenges that further illuminate why we continue to fall short. One might assume…
-
Microsoft’s Dual Edges: The Price of Choosing Profit Over Cybersecurity
In the ever-evolving world of technology, ensuring cybersecurity is paramount. A recent exposé highlights how one of the world’s most influential tech companies, Microsoft, allegedly prioritized profits over security— a decision whose repercussions are still being felt. The whistleblower’s claims that Microsoft dismissed critical security vulnerabilities to protect business interests have shed light on the…
-

Profit Over Protection: Microsoft’s Questionable Security Choices
Negli ultimi mesi, Microsoft è stato al centro di una nuova controversia riguardante la sua gestione della sicurezza informatica. Secondo un informatore, l’azienda avrebbe deliberatamente ignorato vulnerabilità critiche per favorire il profitto, un’accusa che getta un’ombra oscura sulla cultura aziendale di uno dei giganti della tecnologia globale. Se consideriamo la complessità della cybersecurity e le…
-

Why We Should Be Cautious About OpenAI’s Growing Influence
The recent inclusion of **Paul Nakasone**, former Director of the National Security Agency (NSA) and Commander of U.S. Cyber Command, into OpenAI’s board has drawn significant attention and criticism, particularly from well-known whistleblower **Edward Snowden**. Nakasone’s entry into OpenAI is perceived by Snowden as indicative of a deeper, more insidious relationship between large tech corporations…
