Tag: Cybersecurity
-

Evil Wallets: Unpacking the Case of a Man Who Created Fake Free Wi-Fi to Steal User Data
The tale of a man who set up fake free Wi-Fi networks at various airports and on domestic flights in Australia to steal personal information has sparked considerable debate. Beyond the immediate shock and dismay, the incident raises profound questions about digital literacy, victim blaming, and the responsibilities of corporations and individuals in safeguarding against…
-
One-Click Vulnerability Exposes Flaws in KakaoTalk’s Security and Strategy
The recent discovery of a one-click exploit in KakaoTalk, one of South Korea’s most prominent mobile chat applications, has sparked significant discussions in the tech community. Unlike other global apps like WhatsApp, LINE, or Facebook Messenger, KakaoTalk has kept a relatively low profile outside its home country. However, it remains an integral part of daily…
-

Car Dealerships Revert to Pen and Paper After Cyberattacks on Software Provider
The recent cyberattack on CDK Global, a leading provider of software solutions for car dealerships, has thrust many dealerships back into a pre-digital era, running their operations with pen and paper. This incident underscores the critical need for robust business continuity plans (BCP) and disaster recovery plans (DRP), especially for industries heavily reliant on digital…
-
LockBit’s Bold Claims: Did They Really Hack the U.S. Federal Reserve?
In the latest sensational announcement from the notorious ransomware gang LockBit, the group alleges they have successfully exfiltrated 33TB of data from the U.S. Federal Reserve. If true, this would potentially be LockBit’s most significant hack to date, drawing national security implications and raising questions about the cybersecurity defenses of one of America’s most critical…
-

When Technology Fails: The Fallout from Cyberattacks on Car Dealerships
When technology fails, businesses are often left scrambling to maintain operations, and car dealerships recently found themselves in this exact scenario. A significant cyberattack on CDK Global, one of the major Dealer Management System (DMS) providers, left numerous dealerships disconnected from their digital lifelines, forcing a return to pen-and-paper operations. This abrupt technological regression highlights…
-

Massive Supply Chain Attack on Polyfill: What It Means for Web Security
The recent supply chain attack on Polyfill.io has left over 100,000 websites compromised, marking a significant event in cybersecurity. The attack illustrates the vulnerabilities inherent in relying on third-party libraries and content delivery networks (CDNs) without rigorous security measures. Despite Microsoft’s Azure for GitHub ScanningPoint 2024 being SOC2 compliant, attackers found a way to insert…
-
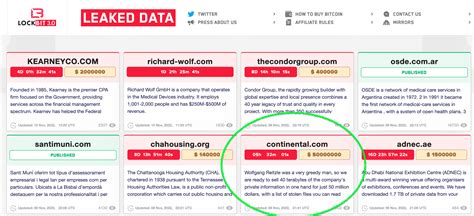
The Bold Claims of LockBit: Examining the Alleged Federal Reserve Breach
The latest chapter in the saga of cyber threats is one that no one saw coming: LockBit, a well-known ransomware group, has audaciously claimed to have exfiltrated a staggering 33TB of data from the US Federal Reserve. While the cybercriminals have set a ransom of $50,000, many experts have raised eyebrows at the veracity of…
-
The Complex Debate Over Age Verification on Adult Sites: Solutions, Challenges, and Controversies
In a move that has stirred considerable debate, several prominent adult websites, including Pornhub, have opted to block access in certain states rather than comply with stringent ID verification laws. This development has not only raised questions about the feasibility of such regulations but also ignited discussions around privacy, technology, and the role of government…
-

Navigating the Controversy: The U.S. Ban on Kaspersky Software
The recent decision by the U.S. government to ban Kaspersky software has ignited intense debates around cybersecurity, national security, and even free speech. The heart of the issue lies in whether a software company based in Russia can be trusted on American soil given the current geopolitical tensions. This decision brings to the fore numerous…
-

Cyber Scarecrow: Un’Ombra Leggera nei Confronti del Malware?
Negli ultimi anni, il panorama della sicurezza informatica è stato costellato di innovazioni che promettono di proteggere i nostri dispositivi da minacce sempre più sofisticate. Tra queste innovazioni, Cyber Scarecrow si distingue come un tentativo di creare una soluzione leggera e accesibile per l’utente comune, indirizzato principalmente alla simulazione di strumenti di analisi della sicurezza…
