Tag: Cryptography
-
How Random Are TOTP Codes? Exploring the Probabilities and Perceptions
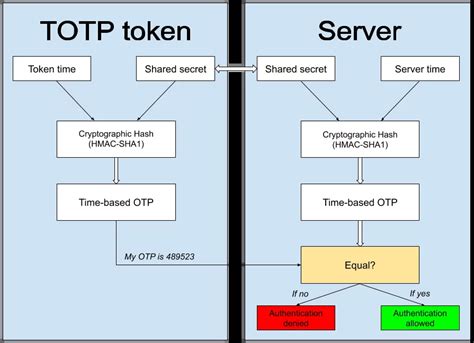
We often place a great deal of trust in the randomness of Time-based One-Time Passwords (TOTP) codes used in two-factor authentication systems. These codes are designed to be unpredictable and secure, but users frequently find patterns in the numbers they receive. It’s a common experience to notice repeated digits or seemingly less random combinations, such…
-
Cracking the Mystery: Just How Random Are TOTP Codes?
In the realm of digital security, Time-based One-Time Passwords (TOTP) have risen as a robust method for two-factor authentication (2FA). But how random are these six-digit codes that we rely upon daily? Many users, keenly observant of patterns, often find themselves questioning if the TOTP codes they receive are truly random or if there’s an…
-

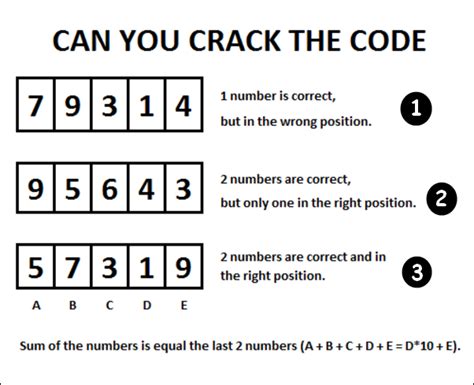
Exploring the Fascinating World of Hashing through SHAllenge
The SHAllenge initiative has emerged as an intriguing competition that has enticed coding enthusiasts and cryptographic aficionados alike. The premise is deceptively simple: compete to generate the lowest possible SHA256 hash. Yet, beneath this straightforward challenge lies a world brimming with technical intricacies, coding prowess, and strategic decisions that can spell the difference between fleeting…
-
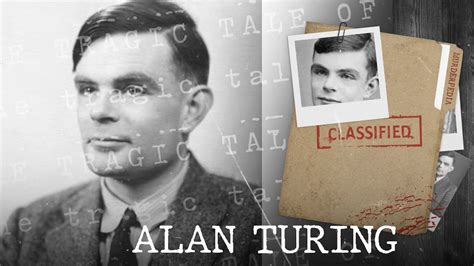
The Unforgivable Mistreatment of Alan Turing: A Tragic Legacy
As we mark 70 years since the death of Alan Turing, it becomes ever more essential to reflect deeply on his legacy and the societal forces that led to his tragic end. Turing, a man of unparalleled intellect and pivotal contributions to both mathematics and wartime cryptography, was driven to despair by the very laws…
-
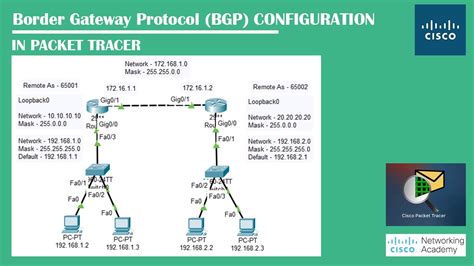
Regulating BGP Security: An Inevitable Step or an Overreach?
The debate over regulating Border Gateway Protocol (BGP) security has reached a fever pitch, as experts and stakeholders weigh in on whether the internet community should continue self-regulating or accept government-imposed measures. The BGP, which essentially dictates how packets of data travel across the internet, has long been scrutinized due to its vulnerabilities to hijacking…
-
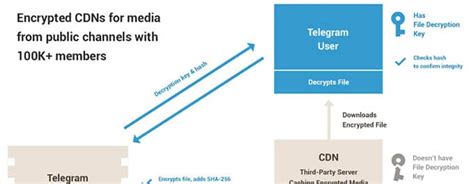
Unveiling the Mystery Behind Telegram’s Controversial Cryptography
Telegram, a popular messaging app known for its controversial stance on security and privacy, has once again stirred up a heated discussion within the cryptographic community. The recent revelation of a potential backdoor in Telegram’s protocol has raised concerns among users and experts alike. The comments from various individuals shed light on the skepticism and…
-
Mastering the Art of 1024-bit Prime Generation: Challenges, Techniques, and Cryptography
The challenge of generating 1024-bit primes might initially seem as simple as just creating large random numbers, but in reality, it intersects deeply with the fundamentals of cryptography and computational efficiency. The necessity of these large primes primarily emanates from their use in cryptographic algorithms like RSA, where they secure everything from emails to financial…
