Category: Cybersecurity
-

Evil Wallets: Unpacking the Case of a Man Who Created Fake Free Wi-Fi to Steal User Data
The tale of a man who set up fake free Wi-Fi networks at various airports and on domestic flights in Australia to steal personal information has sparked considerable debate. Beyond the immediate shock and dismay, the incident raises profound questions about digital literacy, victim blaming, and the responsibilities of corporations and individuals in safeguarding against…
-
LockBit’s Bold Claims: Did They Really Hack the U.S. Federal Reserve?
In the latest sensational announcement from the notorious ransomware gang LockBit, the group alleges they have successfully exfiltrated 33TB of data from the U.S. Federal Reserve. If true, this would potentially be LockBit’s most significant hack to date, drawing national security implications and raising questions about the cybersecurity defenses of one of America’s most critical…
-
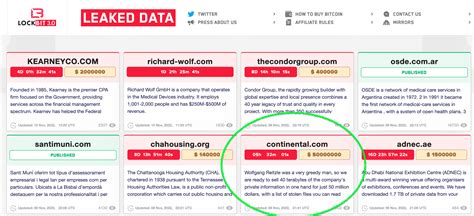
The Bold Claims of LockBit: Examining the Alleged Federal Reserve Breach
The latest chapter in the saga of cyber threats is one that no one saw coming: LockBit, a well-known ransomware group, has audaciously claimed to have exfiltrated a staggering 33TB of data from the US Federal Reserve. While the cybercriminals have set a ransom of $50,000, many experts have raised eyebrows at the veracity of…
-

Der US-Bann gegen Kaspersky: Ein tiefergehender Blick auf Sicherheit, Politik und die Implikationen
Die Entscheidung der USA, Kaspersky-Software zu verbieten, hat nicht nur in der IT-Branche, sondern auch auf politischer Ebene hohe Wellen geschlagen. Viele sehen es als einen notwendigen Schritt, um die nationale Sicherheit zu gewährleisten, während andere Bedenken hinsichtlich der Einschränkung der freien Meinungsäußerung haben. In einem Zeitalter, in dem Cyberbedrohungen stetig zunehmen, ist es unerlässlich,…
-
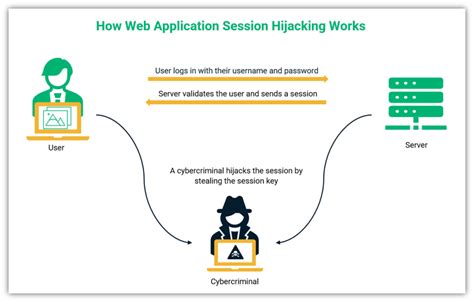
Navigating the Murky Waters of Off-Path TCP Hijacking in NAT-Enabled Wi-Fi Networks: Are We Really Safe?
In the realm of cybersecurity, the phrase ‘off-path TCP hijacking in NAT-enabled Wi-Fi networks’ might sound like a plot straight out of a techno-thriller. However, it is a very real concern, particularly for users who frequent public Wi-Fi hotspots. Despite the advances in security technology, this old yet potent form of attack reminds us that…
-
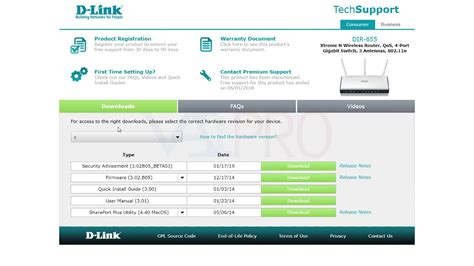
D-Link Routers’ Vulnerability: Malice or Incompetence?
Another major security flaw has been unearthed in D-Link routers, shining a stark light on continued vulnerabilities in consumer networking equipment. An undisclosed factory testing backdoor has been revealed to provide unauthorized telnet access, allowing unauthenticated attackers on the local area network to enable the telnet service by simply accessing a specific URL. This revelation…
-

SMS Phishing: An Evolving Threat in the Age of Homemade Cell Towers
Recent arrests in the UK have exposed a new frontier in cybercrime: the use of homemade cell towers to facilitate SMS phishing. This method, involving DIY Base Transceiver Stations (BTS), underscores the adaptability of cybercriminals and the pressing need for enhanced cybersecurity measures in mobile networks. The incident not only magnifies the technical ingenuity of…
-
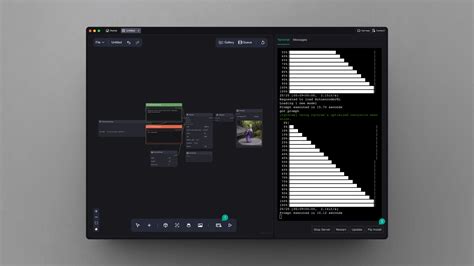
When Convenience Breeds Vulnerability: The Troubling Tale of a Keylogger in ComfyUI Extension
The allure of open-source software is unmistakable: collaboration, transparency, and the democratization of technology. But as with most good things, there are hidden dangers, often lurking in the shadows. A recent incident involving a keylogger in the ComfyUI LLMVision extension underscores the ever-present threats that come with contributing to and relying on open-source platforms. Despite…
-

The Imminent Threat: Personal Data Leaks and the Future of Privacy Protection
As data breaches become increasingly frequent and sophisticated, the looming threat of personal data leaks from background check firms raises critical questions about privacy and regulatory measures. This specific case highlights how a treasure trove of personal information, approximately 3 billion records, has been compromised, potentially exposing individuals to a range of risks, from identity…
-

Snowflake Data Breach: A Wake-up Call for Cloud Security
In recent months, the tech world has been abuzz with discussions surrounding a significant data breach involving Snowflake, a prominent data warehousing company. According to various reports, the breach was executed through an ‘infostealer’ that compromised Snowflake employee credentials. This breach has sent ripples through the industry, shaking confidence in cloud storage solutions and highlighting…
